Is it better to hire or outsource your IT department? While both approaches have their merits, outsourcing can be an attractive option for keeping costs down while maintaining flexibility and reducing risk.
Continue readingConsidering a Managed IT Service Provider? Here are 5 Questions You Need to Ask
Choosing the right Managed IT Services Provider (MSP) is crucial for any business to thrive. But with so many providers to choose from, how do you know which one is right for you? Kirk ISS has provided a helpful guide of five key questions to ask prospective MSPs before signing an agreement. From defining the scope of the agreement, to response times and on-site support, finding an MSP that aligns with your business needs is essential. With a team of on-island experts certified in a range of IT disciplines and an inventory of spare parts at their fingertips, Kirk ISS offers a flexible and personalized approach to IT services and support.
Continue readingKirk ISS Named 2024 Microsoft Cayman Islands Partner of the Year

Kirk ISS Named Microsoft's 2024 Country Partner of the Year in the Cayman Islands
Prestigious award underscores expertise and innovation in Microsoft powered technology.
Kirk Information Solutions and Services (Kirk ISS) today announced it has won the 2024 Microsoft Partner of the Year Award for the Cayman Islands. The company was honored among a global field of top Microsoft partners for demonstrating excellence in innovation and implementation of customer solutions based on Microsoft technology.
Upon learning of the award, Managing Director, Geoff Cuff acknowledged the hard work that goes into being a global leader in the Microsoft space: “We’re thrilled to be recognized again as the premiere Microsoft partner in the Cayman Islands. As the IT landscape continues to evolve, our dedicated Microsoft engineers have been hard at work staying at the forefront of Microsoft’s powerful technologies and helping our customers achieve more every day. I’m very proud of what our team has been able to achieve for our customers who depend on us to get their IT solutions right the first time, every time.”
The Microsoft Partner of the Year Awards recognize Microsoft partners that have developed and delivered outstanding Microsoft Cloud applications, services, devices, and AI innovation during the past year. Awards were classified in various categories, with honorees chosen from more than 4,700 nominations from more than 100 countries. Kirk ISS was recognized for providing outstanding Microsoft security solutions in the Cayman Islands.

“Congratulations to the winners and finalists of the 2024 Microsoft Partner of the Year Awards!” said Nicole Dezen, Chief Partner Officer and Corporate Vice President at Microsoft. “The momentum generated by numerous AI & Copilot announcements this year fueled innovation from our partners, enabling groundbreaking services and solutions to customers. I am inspired by the capability and creativity in our partner ecosystem and this year’s winners beautifully demonstrate the best of what’s possible with AI and the Microsoft Cloud.”
The 2024 Microsoft Partner of the Year Awards are announced ahead of MCAPS Start 2024 Microsoft Partner of the Year Awards press release guidelines for Partners, our digital event on July 10th and 11th. Partners will receive recognition at MCAPS Start for Partners ahead of in person celebrations during the week of Microsoft Ignite in November. Additional details on the 2024 awards are available on the Microsoft Partner blog: https://aka.ms/POTYA2024_announcement. The complete list of categories, winners and finalists can be found at https://aka.ms/2024POTYAWinnersFinalists.
Unleash the Power of Continuous Learning with Microsoft Viva
Unleash the Power of Continuous Learning with Microsoft Viva
In the dynamic landscape of today’s professional world, continuous learning has become a cornerstone for personal and organisational growth. Microsoft Viva Learning, introduced as part of the Microsoft Viva platform, aims to revolutionise the way companies approach employee development. This article will delve into the key features, architecture, and benefits of Microsoft Viva Learning.
Microsoft Viva Learning is an integrated learning platform designed to centralise and simplify the learning experience for employees within Microsoft 365. It brings together various learning resources, content, and tools, creating a unified hub for continuous development.
Unified Learning Hub
Viva Learning integrates seamlessly with Microsoft Teams, providing a unified learning experience within the familiar Teams interface. Employees can access learning resources, courses, and training materials without switching between different platforms.
Content Aggregation
Viva Learning aggregates content from various sources, including LinkedIn Learning, Microsoft Learn, and third-party providers. This enables organisations to leverage a wide range of resources to meet diverse learning needs.
Key Features of Microsoft Viva Learning:

Personalised Learning Paths
Viva Learning uses AI to analyse employee skills, roles, and preferences to recommend personalized learning paths.
This feature ensures that employees receive relevant content tailored to their individual development goals.
Integration with Microsoft Teams
The integration with Teams makes learning a seamless part of the daily workflow.
Team leaders can assign and track learning tasks directly within Teams, fostering a collaborative and engaging learning environment.
Rich Analytics and Insights
Viva Learning provides analytics dashboards for administrators to track employee engagement, completion rates, and overall learning progress.
Insights gained from these analytics enable organisations to make data-driven decisions about their training programs.
Real-Time Updates and Adaptive Learning Thanks to AI

Microsoft Graph API Integration
Viva Learning leverages Microsoft Graph API to integrate with various data sources within Microsoft 365. This integration allows for real-time updates and ensures that learning content is always up to date.
Adaptive Learning with AI
The AI capabilities of Viva Learning enable adaptive learning experiences. Machine learning algorithms analyse user behaviour, learning patterns, and feedback to continually refine and improve the learning recommendations.
Benefits for Organisations

Improved Employee Engagement
By integrating learning seamlessly into the Teams environment, Viva Learning enhances employee engagement with training materials.

Efficient Training Management
Team leaders and administrators can manage training initiatives more efficiently through the centralised dashboard and reporting features.

Flexibility and Scalability
Viva Learning’s ability to aggregate content from various sources ensures flexibility and scalability for organisations with diverse learning needs.
A Powerful Learning Platform
Microsoft Viva Learning represents a significant leap forward in the realm of employee development. By combining the power of Microsoft 365, Teams integration, and AI-driven personalisation, it offers a comprehensive solution for organisations looking to foster a culture of continuous learning. As businesses navigate the ever-evolving landscape, embracing platforms like Viva Learning becomes instrumental in staying competitive and empowering employees for success.
Get Guidance and Support from our Microsoft Experts


As a Microsoft Modern Work Solutions Provider and 5-time Microsoft Partner of the Year, we have the know-how and experience to make the most of Microsoft solutions for your business. Our team can help you boost productivity with Microsoft products such as Microsoft Azure, Microsoft Defender, Microsoft Office 365, Enterprise Mobility Suite, Microsoft Viva and Windows. Get in touch today to schedule a free 1-on-1 needs assessment.
9 Benefits of Managed IT Services: Grow Your Business the Smart Way
More than ever, modern businesses are faced with growing challenges and increasing complexity. Learn how to leverage the expertise of an entire team of IT experts to grow your business while cutting costs.
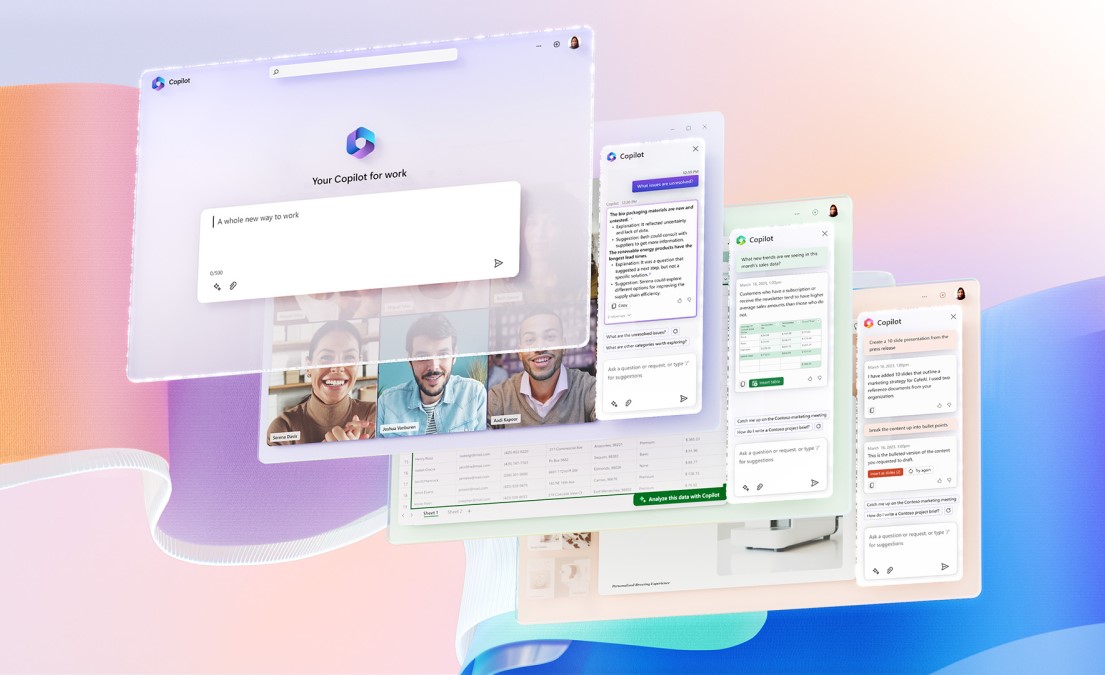
Continue readingMicrosoft Copilot, Your Everyday AI companion
AI powered tools can help to make your team more productive and efficient. In this post, we take you through some of the key features of Microsoft Copilot.
Continue readingCyber Security Best Practices – Quick Wins for Better Security
Cybersecurity Best Practices: Quick Wins for Better Security
In light of the rapid changes in the the volume and sophistication of modern threats, organisations need to focus on cybersecurity more than ever. Developing a robust cybersecurity framework that cascades throughout the business is paramount to ensuring the remote workforces are as protected as their office counterparts. For most organisations, the cybersecurity foundation starts with simple, yet sensible data protection policies and rules that are consistently enforced.
Here are a few quick and easy ways to bolster your organisation’s cybersecurity:

Develop Formal IT Policies and Procedures
Almost every industry has some form of regulatory guidance for organisations to adhere to. Financially regulated entities have items like CIMA’s statement of guidance, vendors and retailers must adhere to Payment Card Industry (PCI), and every organisation needs to be aware of the EU’s General Data Protection Regulation (GDPR). Creating formal IT policies and procedures goes beyond rules for employees to follow when using their work computers – it creates a foundation for the organisation to operate should it need to recover from a disaster or plan for business continuity, how they mange their third-party affiliates and vendors, and how they plan on responding to cybersecurity threats and incidents.
 Train Cyber Ninja Employees
Train Cyber Ninja Employees
*In 2021, nearly 85% of data breaches involved some form of human element to gain entry into a network. Training your staff how to identify threat is key to preventing a cybersecurity incident from occurring. The best training doesn’t happen in a vacuum – the cyber threat landscape evolves constantly, requiring at least annual refreshers for employees to be set up for success. Our cybersecurity team conducts regular End User Awareness Training, along with simulated Social Engineering Assessments to proactively identify areas to strengthen.
 Tighten Cloud-Based Platforms
Tighten Cloud-Based Platforms
Work from home is rapidly evolving into work from anywhere. With BYOD becoming the norm for more and more organisations, it’s important to employ effective mobile access policies. Spending time to review cloud-based platforms, such as Microsoft Azure and Office 365 controls will help define security baselines to ensure resources are protected no matter where they are stored. Some controls should include the use of Multi-Factor Authentication (MFA), password managers, Conditional Access policies, compliance and configuration baselines, remote management of devices, and identity protection for users and corporate resources alike. Kirk ISS regularly reviews customer baselines during our Infrastructure Audits to uncover gaps in configurations, helping strengthen their cybersecurity posture.
 Think Like an Adversary
Think Like an Adversary
Regardless of whether you believe that “offense wins games, but defense wins championships”, the truth is there are more attackers than there are defenders in the cybersecurity workforce. *Gartner reports that in 2019, there was a deficit of nearly 65% between roles waiting to be filled and the talent pool of cybersecurity professionals. What does this mean for you? Small to medium business may not have the budget or need for a fully-fledged cybersecurity team to proactively monitor, identify, and respond to threats like large organisations, but the need is there. Kirk ISS offers a Managed Detection and Response service to provide budget-friendly, cost effect methods of providing proactive cyber threat monitoring. In addition, assessments like Network Security Assessments have our cybersecurity professionals simulate hacking activities to uncover vulnerabilities before they can be exploited by the real bad guys.
Balancing Security with Productivity
Cybersecurity has become ubiquitous with the current state of remote work and will continue to be a dominant concern. CIO’s and IT managers will need to strike a balance between driving productivity with the very real need to protect data from an ever-evolving threat landscape. Fortunately, our team of cybersecurity experts can help if you need help deploying any of these best practices to protect your IT systems.
Some of the cybersecurity services we offer:
• 24/7 Managed Detection and Response
• Network Security Assessments
• Policy Creation
• End User Awareness Training
• Infrastructure Audits
* 2021 Verizon DBIR (https://enterprise.verizon.com/resources/reports/2021-data-breach-investigations-report.pdf)
* https://www.gartner.com/en/human-resources/research/talentneuron/labor-market-trends/cybersecurity-labor-shortage-and-covid-19
Microsoft 365 Defender Named Forrester Leader for XDR
Microsoft named a Leader in The Forrester New Wave™: Extended Detection and Response (XDR) category.
Continue reading5 Ways to Overcome Cybersecurity Challenges in Uncertain Times
5 Ways to Overcome Cyber Security Challenges in Uncertain Times
According to the World Economic Forum’s The Global Risks Report 2021, cyber threats are among the leading global risks.
With remote and hybrid work changing the landscape of how businesses operate, new vulnerabilities have emerged practically overnight. Hacks are now more commonplace due to the rise of mobile usage and internet of things (IoT). Data protection compliance has become more complex with the introduction of regimes like GDPR. And, to compound this, a growing ecosystem of cybercriminals are more technologically savvy than ever – resulting in sophisticated cyberattacks that can get around an organisation’s employees, firewalls or SIEM software, and cost companies millions of dollars.
There’s no doubt that cybersecurity is something to pay attention to. It’s an issue that’s made its way into the boardrooms of companies large and small, impacting even the world’s most prominent financial and healthcare organisations.
Now more than ever, it’s crucial to understand and develop strategies to overcome cybersecurity challenges. Here are five ways to prepare yourself and your company, so you can strengthen your cybersecurity posture and be future-ready.
1) Understand How Cybercime Tactics Have Evolved
Cybercriminals are opportunists. New technology, processes and practices are always being developed. And, at the same time, threat actors–including ransomware groups and adversarial governments–are constantly adapting their ways to circumvent security measures.
Though cybercriminals are usually money, some also want to expose data and confidential information or simply degrade a company’s reputation.
The most common types of cybercrime tactics include:
- Distributed denial of service (DDOS): A disruption of network service where attackers send high volumes of data through a network, which then becomes overloaded and stops working.
- Phishing: When cybercriminals “fish” for data from third parties, usually via email. These phishing emails are becoming increasingly sophisticated, so much so that some of them require cybersecurity experts to distinguish them as phishing.
- Malware: Also known as malicious software, malware comprises over one half of all cybercrimes. It’s designed to gain access to a computer or network, and is often introduced via email attachments, software downloads or OS vulnerabilities.
- Internal privilege misuse: This is when an opportunistic employee secretly steals or leaks confidential information for monetary gain. They can also take personal information, including healthcare data, for financial crimes or identity theft.
The COVID-19 pandemic intensified the rate of cyberattacks. As companies were forced to experience rapid digital transformation and implement remote work arrangements, cracks appeared which cybercriminals knew they could exploit.
Even though it’s been more than two years since the pandemic began, many overworked and unprepared IT departments are still struggling to keep up with security demands. Employees are still logging into corporate networks from unsecured computers. And cybercriminals have found ways to target software like Zoom and Microsoft Teams.
Cybercriminals also take advantage of urgency. During the pandemic, Cayman experienced a spike in phishing attacks and malware, which was largely due to cybercriminals exploiting people’s fear of medical equipment shortages, and the urgent need for fundraising.
Finally, for the most part, cybercriminals operate worldwide and know no borders. A crop of “corporate cybercriminals” has emerged, who are more savvy and have access to extensive resources to pivot quickly – taking advantage of vulnerabilities.
The first step to keeping your company secure is to understand–and stay on top of–these trends.
2) Prioritise Cloud and Endpoint Security
Cloud and hybrid OS and data systems are here to stay. This has caused unique challenges for companies that have traditionally operated using on-premise networks.
The good news is that cloud networks are often more inherently secure than on-premise networks, but customers need to understand that they have a shared responsibility for cloud security. Failing to recognise this can lead to costly outcomes. In fact, Gartner predicts that through 2025, 90% of the organisations that fail to control public cloud use will inappropriately share sensitive data.
Adding to the complexity is the rise of BYOD (bring your own device) and remote work policies. This raises concerns around endpoint protection. Simply put, an endpoint is one end of a communication channel, and in a workplace context involves items like laptops, mobile devices, tablets and printers. Cybercriminals can exploit unprotected endpoints and use them as an entry point into your network.
As cloud infrastructures grow, and more companies enter into hybrid cloud and remote work scenarios, it’s important for companies to prioritise cloud and endpoint security.
3) Embrace End-User Cyber Security Training
The biggest security gaps usually lay with end-users. In fact, according to Gartner, 99% of cloud security incidents through 2025 will be due to end-user errors. That means it’s important to create a corporate cybersecurity policy that includes comprehensive end-user training.
Developing employee knowledge around what to watch for, how cybercrime works and cybersafe best practices will go a long way in ensuring your company and your employees are protected.
End-user training can include:
- How to recognise phishing and social engineering attacks
- Best practices to manage passwords
- Steps to keep devices and endpoints secure
- How to avoid malware and ransomware attacks
- Physical security tips, such as device and document locking
4) Recruit Top IT Talent
According to a 2021 study by Gartner, the biggest barrier to adopting new technology is a lack of talent. This is especially the case when it comes to security technology and cybersecurity talent.
Compounding this problem is the fact that IT budgets are often stretched thin. When resources are limited, companies tend to put them towards supporting day-to-day needs, rather than towards measures that are preventive or proactive. Unfortunately, it often takes a breach or cybersecurity incident to occur before companies will invest in cybersecurity talent.
Of course, “talent” doesn’t necessarily mean every employee needs to be a cybersecurity expert. It means finding and fostering a team that’s keen to learn and adopt new technologies, committed to staying current on cybersecurity threats and that’s generally aware of cybercrime tactics.
If you’re unable to find the right talent, outsourcing this role to an expert is another option. That takes us to our final point.
5) Consider Hiring Cyber Security Experts to Support Your Team
With competing priorities and technology continually evolving, IT departments are stretched thin.
Although guidance documents – such as Cayman’s Statement of Guidance: Cybersecurity for Regulated Entities – are available to support cybersecurity teams, they can be difficult to implement alone.
As a result, it can be cost-effective to utilise a managed cybersecurity service or IT security partner. Good cybersecurity experts are up-to-date on the latest issues, are ready to get your organisation compliant with regulations like GDPR, HIPAA or Cayman’s data protection legislation, and can create and monitor your systems with advanced SIEM software.
Outsourcing your cybersecurity to experts who are already well-versed in all aspects of your security needs – including policies, infrastructure, cloud services and other services – can also free up time for your IT team to focus on key strategic priorities.
Partner with Kirk ISS and Take Control of Your Cyber Security
If you’re seeking a cybersecurity partner to help keep your business safe, Kirk ISS is here to help. We offer a full range of cybersecurity services including:
Cyber Security Assessments
Get a comprehensive review of your organisation’s cyber security posture, highlighting gaps in your defenses and recommending specific steps to remediate them. Help satisfy data protection regulations and stay compliant.
- Cybersecurity risk assessments
- Penetration testing
- Office 365 security assessment
End-User Training
Get a comprehensive review of your organisation’s cyber security posture, highlighting gaps in your defenses and recommending specific steps to remediate them. Help satisfy data protection regulations and stay compliant.
- Cybersecurity risk assessments
- Penetration testing
- Office 365 security assessment
Managed Threat Detection & Response
Get a comprehensive review of your organisation’s cyber security posture, highlighting gaps in your defenses and recommending specific steps to remediate them. Help satisfy data protection regulations and stay compliant.
- Cybersecurity risk assessments
- Penetration testing
- Office 365 security assessment
Serving the Cayman Islands since 2005, our team of IT experts can help keep your data safe, your employees protected and your operations running smoothly.
To learn more or book a free discovery call, contact us today.
Kirk ISS Named 2022 Microsoft Partner of the Year
[GEORGE TOWN, Grand Cayman], [Cayman Islands] — June 28, 2022 — Kirk Information Solutions and Services (Kirk ISS) today announced it has won the 2022 Microsoft Country Partner of the Year Award for the Cayman Islands. The company was honored among a global field of top Microsoft partners for demonstrating excellence in innovation and implementation of customer solutions based on Microsoft technology.
As Managing Director Geoffrey Cuff explains, being awarded Partner of the Year from Microsoft is an important accomplishment for his team: “We are thrilled to have been recognized as the top solutions provider in the country yet again by a global leader like Microsoft. This award is thanks to the exceptional work of our IT engineering and customer success teams who work tirelessly to deliver world-class solutions to our customers. As a team, we couldn’t be more pleased with this significant achievement.”
The Microsoft Partner of the Year Awards recognize Microsoft partners that have developed and delivered outstanding Microsoft-based applications, services and devices during the past year. Awards were classified in various categories, with honorees chosen among more than 3,900 submitted nominations from more than 100 countries worldwide.
The Microsoft Country Partner of the Year Award acknowledges outstanding achievements and innovations from Microsoft partners at the country level, recognizing partners that have built solutions and services on the Microsoft cloud and who have had substantial growth in their customer base and/or revenue.
This year Kirk ISS was recognized for delivering security-centric Microsoft solutions in the Financial Services industry, a vital sector of the Cayman Islands’ economy. These solutions used Microsoft technology to secure the systems of financial firms and helped to verify compliance with data protection regulations such as GDPR and the Cayman Islands Data Protection Act.
“I am honored to announce the winners and finalists of the 2022 Microsoft Partner of the Year Awards,” said Nick Parker, corporate vice president of Global Partner Solutions at Microsoft. “These partners were outstanding among the exceptional pool of nominees and I’m continuously impressed by their innovative use of Microsoft Cloud technologies and the impact for their customers.”
 Microsoft Partner of the Year Awards are announced annually prior to the company’s global partner conference, Microsoft Inspire, which will take place on July 19-20 this year. Additional details on the 2022 awards are available on the Microsoft Partner Network blog: https://blogs.partner.microsoft.com/mpn/congratulations-to-the-2022-microsoft-partner-of-theyear-awards-winners-and-finalists
Microsoft Partner of the Year Awards are announced annually prior to the company’s global partner conference, Microsoft Inspire, which will take place on July 19-20 this year. Additional details on the 2022 awards are available on the Microsoft Partner Network blog: https://blogs.partner.microsoft.com/mpn/congratulations-to-the-2022-microsoft-partner-of-theyear-awards-winners-and-finalists
The complete list of categories, winners and finalists can be found at https://partner.microsoft.com/en-us/inspire/awards.